My name is Ilia and I am glad to meet on my blog about Security Engineering , AI automation , and random fun stuff. Check out my recent posts below! And make sure to follow my social networks😉

Navigating Security Operations career path: talk alert🎤
Hi! Recently I did a talk about Security Operations career path at Microsoft Innovation Center Armenia!🤓 Slides📈 You can download the slides here or watch in a widget below: Short agenda of my talk📝 Intro to security teams responsibilities What does SecOps actually do? Big-Picture view on Security Operations Center process What is SIEM and detection engineering? How SecOps responds to threats: playbooks and automations Recovery methods How to obtain SecOps skills - useful resources and certifications‼️ Bonus🎁 I’ve included a few practiacal cases in my presentation to make it less theoretical and out-of-context. Read my presentation If you wonder how SQL-injections look from the defenders side!

Hunting for diamonds💎: What is The Diamond Model?
Hey! I am back with a new cycle of threat huting articles special for you. And in this part we are going to look into the basics of The Diamond Model of Intrusion Analysis and what it is about. I’ll try to keep it solely practical and simple. This thing is pretty popular in jobs requirements and is even implemented inside OpenCTI Platform! Is this a real thing or yet another empty shell? Let’s dive in! ...
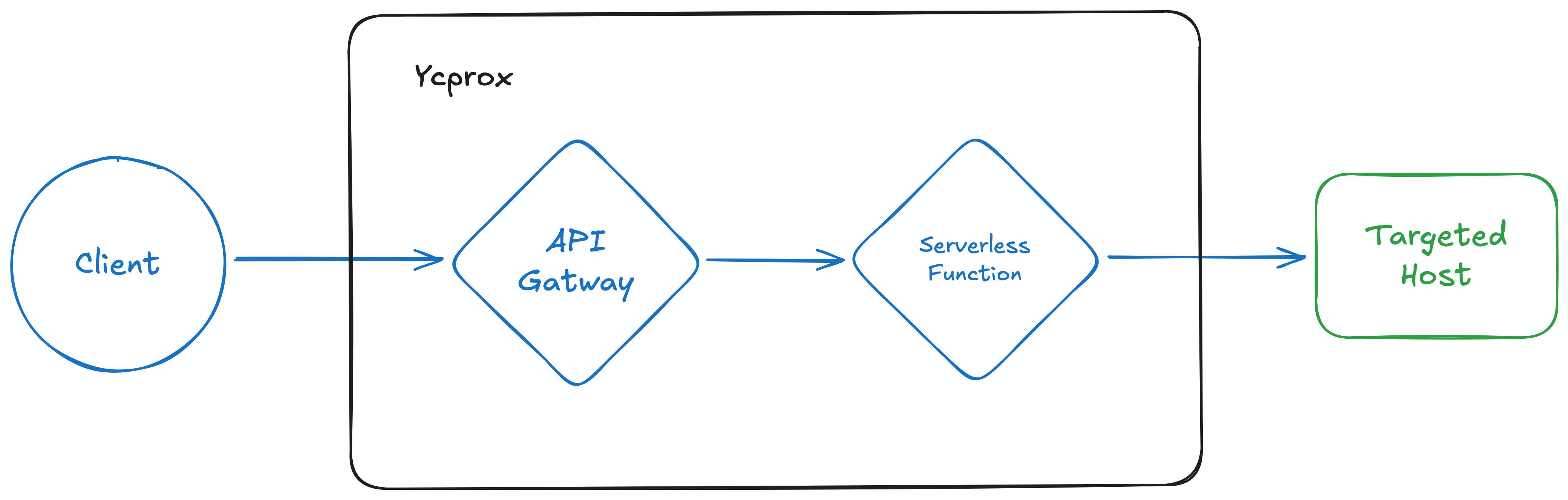
New tool release! Welcome ycprox
Hey! I recently developed a new tool ycprox which allows you to quickly deploy a forward proxy in Yandex Cloud infrastructure to change your IP address (almost) each request. You can check it out on Github and in this post I will cover some particularities I had to tackle / implement during development. The idea💡 Originally I wanted to adapt the existing fireprox project for using Yandex Cloud (YC) resources. Here is how fireprox works in simple terms: ...

Policy 🆚 security alerts or why your SOC is suffering 😵
Do you want to optimize your Mean Time To Response in your SOC? Do not feed your SOC with misconfigurations! What’s the problem?🤔 You see, there are lots of alerts in your SIEM which your SOC analysts have nothing to do with. Examples could be: Unauthenticated service found Publicly available endpoint Password authentication on SSHD Security Operation Center is a great resource to find and contain threats, but very often SOC analysts encounter misconfiguration alerts which tell you only about probability of exploitation, not the malicious behaviour / threat has already occured. ...

How to secure your AWS Lambda: talk alert!🎤
Hey! Recently I’ve presented a talk at BSides Yerevan 2025 about how to attack and defend your AWS Lambda serverless functions. This was my first attending of conference as a speaker and I am proud to be a part of invited speakers pool. Many thanks to CyHub Armenia! I would like to share my slides and demonstration I showed during my presentation. Don’t forget to mention me when using parts of my materials👀 ...
Authentication vs authorization in Zero Trust👀
After authentication goes authorization, right? WRONG!❌ Well… Not immediately. According to ZeroTrust methodologies, you have to dynamically make a decision of authorizing (or not) requests depending on state of your user / device / application and combinations of them🤔 Think of authorization decision as a control plane “brain”, which instead of granting permissions right after authentication considers a few factors: device type: mobile / laptop location of device and / or user history of user-agents application access history of the user NAC-compliane of device etc Why It makes your security less rigid than static policies, more flexible and context-rich. Also instead of simply denying request, you could ask for another auth-factor such as TOTP or SMS code. ...
How to: securely store passwords in DB🔐
Wanna know how to securely store passwords in DB? There is a way to do it more securely than doing SHA256(salt|password). Recently I’ve read a great article about bcrypt and now I will definitely use it to hash passwords🔐 The trick is in ability to control the complexity of hashing passwords so even in case of DB compromise the attackers will be significantly slowed down while brutefocing your hashed passwords👾 Also your passwords will be prune to precomputed rainbow tables because all passwords have their own salt baked into password. ...